Self-Sovereign Identity in the Blockchain Age
Do we really need (or want) the State to provide us with digital identification?

Who are you? In today’s world you can’t get far without an identity, which is attested to by a verifiable identity card or document. You may take this piece of paper or plastic for granted, only realizing just how important it is when you carry it with you through a police checkpoint, make a large bank withdrawal, or check-in at an airport. While that may just be an inconvenience to middle-class citizens of developed countries, it can be a devastating problem for those who cannot credibly prove their identity. Those without a certified identity may face insurmountable barriers to basic financial, social, and political transactions.
From Pre-Modern to Modern Identity
The goal of identity documentation is to generate trust between two people in a transaction. In the pre-modern era, trust could only be extended to the small number of people of whom one had immediate knowledge. That meant the town baker could arrange for credit with the town miller based on their prior knowledge of each other’s reputation for probity; but that trust was severely limited in scope. Building global rather than merely local markets required widening the potential circle of trust to include complete strangers.
As our lives became more complex, encompassing an increasing number of people with whom we interacted, society came up with various “identity-creating” technologies. Those technologies can be used to build a reputation that is linked to identity and thus permits market transactions between strangers. The State has played such a significant role in generating identity technologies that it has made it hard for some to imagine that a purely market-based society could self-generate instruments on its own.
For example, consider the evolution of surnames. In early human societies, first names were sufficient to identify the members of individual clans, sometimes with an additional patronym like Peter Siggurdson, or Peter, son of Siggurd. Later, descriptive second names were added, often derived from the profession of the person—last names such as Baker, Fisher, Miller, and Smith still bear witness to this today.
The early modern State had an interest in institutionalizing these naming patterns in order to make the citizenry “legible,” to borrow a term from James C. Scott, thus making it easier to tax and control citizens of newly enlarged and centralized nation-states. The previously unbound second names became official family names and were made permanent and hereditary even if they no longer coincided with profession. Consequently, state-affixed identity became the basis for most forms of modern identification. Identification was thus no longer just a set of technologies for encouraging trust between strangers but now also a method for extracting rents on behalf of the State.
Identity in a Digital Age
The nature of identification began to shift with the advent of the internet. Today, digital identification can be stored in central data centers operated by the likes of Google, Facebook, or Microsoft and then used to certify a host of online transactions. Just as the State still manages our “analog” identities, the online giants have vast power to manage the online data and identity of their users. Internet users are now both consumer and product: by using free online services, users feed companies with data, which those companies in turn process and monetize.
Some users are content with the exchange of data for online services, but others feel deprived of the added value their data provides to platforms and alienated by their inability to determine how their data is used and by whom. Just as the bankruptcy of Lehman Brothers ushered in the financial crisis of 2008, revelations about the data analysis firm Cambridge Analytica and its influence on the U.S. election campaign marked the starting point of what can be called the data crisis of 2018. The most strident critics feel that nothing less than democracy itself is at stake.
In response, the European Union issued new data protection guidelines in May 2018 called the General Data Protection Regulation (GDPR). It is intended to allow users to find out at any time how a company uses their data, but loopholes and back doors can always be found and there have been many directives announced before GDPR that turned out to be mere paper tigers.
Reducing Dependency with Self-Sovereign Identity
Self-sovereign identity is a sustainable and genuine solution to the data privacy dilemma. Given that we are increasingly part of a global civil society and that we will interact more and more over digital networks in days to come, such a self-governing identity is long overdue. In the future, responsibility for and control over one’s own digital personality will lie with internet users themselves. Just as a person has control over their own self in the physical world, the same should apply to the digital self. We will determine what digital information we share and with whom we share it.
However, there is currently no universal identity layer on the internet. In order to identify oneself, a user must remember a plethora of passwords and access codes. As an alternative, many websites offer the option of logging in with a third-party profile, like Facebook or Google. Identification then takes place via the third party, which is then able to collect further data about the user. Again, users trade control over their data in exchange for a free service, identity verification in this case.
With a self-sovereign identity, dependency on third parties for identification would be reduced. Relevant identity data could be stored on each person’s device, such as a mobile phone. It would also be possible to use so-called identity hubs, which would store and transmit data. However, the operators of such hubs would not have the access keys needed to decrypt the cryptographically secured user data. In addition, users could independently extract the encrypted data at any time.
For self-governing identity verification systems to become reality, it will require the development of new technologies. Public blockchains are an important part of the puzzle because they provide a non-centralized identification management system. So-called “digital identifiers” play a decisive role in this regard; it will one day be possible to assign them directly to users. The identifiers can then be controlled independently via public blockchains. Using a decentralized identifier, an associated DID Document with verifiable claims—essentially decentralized identity cards—users could voluntarily identify themselves at any time without having to rely on a centralized authority.
DIDs could be registered directly on a public blockchain. Unlike in the transmission of value units such as bitcoin, decentralized identifiers are not subject to the double-spend problem. Ultimately, all that is needed is a flawless chronology that is ensured by time stamps on the public blockchain, which acts as an anchor of trust. Metadata adjustments for an identity could be made using an additional protocol. As it so happens, Microsoft has already created an open-source second-layer protocol, called ION (which is comparable to the Lightning Network), that could serve this function.
DIDs are user-generated, self-managed, and uniquely identifiable worldwide. This makes them tamper-proof, resistant to censorship, and virtually unalterable. Theoretically, a new DID could be created for each digital interaction and a pair of DIDs could be generated whenever an internet user contacts another internet user. The goal, however, is for end users to always retain control over their own DIDs and for those DIDs to be based on the data entrusted to the wallet or another identity management application.
In a world where anyone can create an account and any number of DIDs, the question inevitably arises: How can we make sure that a DID-based identity has any value at all, that it really stands for the person it claims to represent? The answer is surprisingly simple. Think of a newly created DID like it is an empty envelope. Now, you could send that empty envelope to almost anybody as long as you had their physical address, meaning that it would be easy for someone else to send an empty envelope to that person while claiming to be you. But if, instead, you sent an envelope packed with pieces of information that only you could have known, it becomes nearly impossible to fake that identity claim.
So too with your DID, which starts out “empty” but is gradually filled with data. This is done piece by piece through various self-made claims; but other users also contribute to the process, including companies, educational institutions, and even governments, by issuing attestations to the DID that this DID represents who it says it does. The more verification and testimonies a DID receives from trustworthy entities, the more trustworthy the decentralized identity itself becomes.
Claims Become Verifiable
The concept behind the DID is called the Verifiable Credential Model. A credential is an attestation of qualification or capability. Examples of paper-based credentials are passports or driver’s licenses. But what if the holder of the credential and the person or organization verifying the credential could get credentials online—perhaps from some of the very agencies that currently provide paper versions— in a fully trustworthy manner?
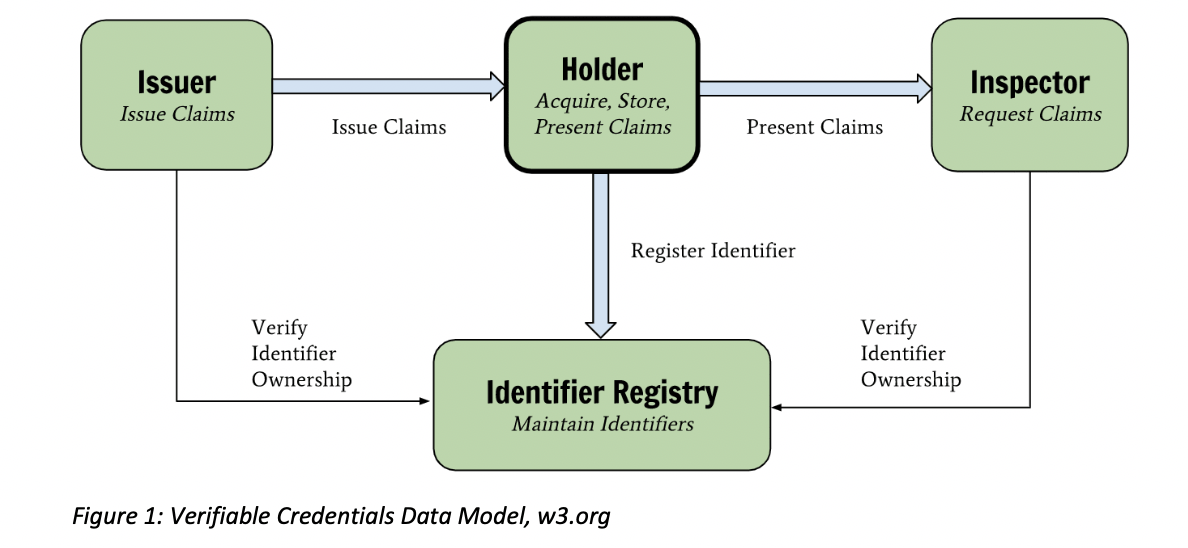
The verifiable credentials model works similar to the paper-based model. Look at the following illustration from the World Wide Web Consortium (W3C); there is an issuer, a holder, and a verifier. After deciding if you are eligible to receive a credential, it is issued to you by a third party which possesses the authority to do so. You hold your credential in your digital wallet. Once you are asked to prove the claims from the credential, you provide a verifiable presentation to the verifier, proving the same things as you would with a paper credential.
Unlike the paper credential model, which depends on the skill of the verifier to recognize a fraudulent credential, the verifiable credentials model includes a data registry—in this case, cryptographic keys and identifiers—that enables the verification of the data. Distributed ledger technologies are well suited to support such a registry.
Verifiable credentials are cryptographically constructed such that presentation of the credential provides four key attributes:
- Who issued the credential.
- That the credential was issued to the entity presenting it.
- That the claims were not tampered with.
- That the credential has not since been revoked.
Unlike a paper credential, those four attributes are evaluated not based on looking at a credential but by cryptographic algorithms. Therefore, verifiable credentials are theoretically vastly more secure than their paper-based predecessors.
However, there remains a challenge facing a verifiable credential that is similar to a problem with paper credentials. To trust the information in a credential, it is necessary that the verifier trusts the issuer. Despite its cryptographic security, the value of a digital version is bound to the issuer’s capability to issue a truthful credential that is accepted by the verifying party.
Yet there is a new set of innovative technologies known as “social proof systems” that are trying to make it possible for people to have their credentials issued in a peer-to-peer manner. Such ideas are still in their infancy, but they hold promise since they would not depend on large central entities to function but could instead utilize the decentralized network of one’s own peers.
Impact of Verifiable Credentials
Once verified, the information contained in such a credential can be trusted to be authentic. That is a powerful attribute! In addition, apart from allowing full control and improved security, these credentials also allow for something called minimum information disclosure. That means that holders can prove the validity of the issuer’s signature without revealing other values that were not relevant to the agreed upon transaction.
For sake of comparison, map that technology onto a credential most people are already familiar with. If you have a government-issued driver’s license, anybody who you hand that card to, like a police officer or bank clerk, can glean significant personal information--eg, organ donor status--from that document that is not strictly necessary to identify you in every case. But imagine if you could “show” your hypothetical digital driver’s license without revealing any personally identifiable information and yet still prove that you’ve been granted permission to drive. That’s a key advantage that the new system would have over our current, outdated verification documents.
Issuers exercise control and gain accountability by possessing the power of immediate revocation. A worker can be issued a professional accreditation credential from the relevant authority; and should the worker lose his or her accreditation, the credential can be revoked immediately and be instantaneously verified by any entity involved.
But verifiable credentials go beyond identity. They would enable the digitization of almost any paper-based verification process. For example, regulatory processes that now involve manually verified paper submissions could be transformed. As these credentials provide instantly authenticatable data, these submissions could verified in real-time. The same applies to data exchange between companies or devices. The verifier could accept the presented claims without the need to check further with the issuer. Instead, the verifier could automatically process the claim and skip a costly and time-consuming back-and-forth with issuers.
Turn Data Into Money
Digital identities also provide hope that it might one day no longer be large corporations that profit the most from user data, but that instead each and every individual user will have the ability to turn their own data into meaningful income. Since people exclusively control their own data with self-sufficient identities, they should be able to share it with interested customers from the field of digital marketing via the public blockchain and perhaps even sell it via open marketplaces to earn money.
But are monetary incentives strong enough to encourage ordinary users to sell their own data? Although estimates vary, a typical Western user might be able to get a couple hundred dollars a year from selling their data. That may not seem like much, but many people are excited about the prospect. And we should expect that dollar value to grow with time as more people plug into online networks and more and more of our lives and work transition online. Perhaps one day, a small basic income could be achieved via self-sovereign digital identities. And in contrast to conventional attempts to instate a universal basic income via the political process, digital identities and the monetization of one’s own data may be able to fulfill the financing of such an income in a self-sustaining, non-State-enhancing way.
However, there are concerns about the monetization of personal data. Don’t data companies earn money with their users’ information precisely because they process and refine the data and thus create added value? Doesn’t our data only become valuable when it is aggregated, turned into big data?
A few years ago, researchers at the University of Cambridge and Stanford University found in a study that a computer could predict a subject’s personality more accurately than an actual work colleague by analyzing only 10 Facebook “likes;” and given 300 likes, it could do even better than a spouse. At some point, this kind of AI (and thus Facebook) could know you even better than you know yourself! So it’s entirely possible that a social network is in a better position to monetize our data and thus our identities.
Digital Nation versus Nation State
States might not welcome the advent of self-sovereign identity for their citizens. The State is, after all, a jealous sovereign. Self-sovereign identity would enable greater protection of the private sphere and at the same time call into question existing identity verification institutions, including the State. Although governments are involved in the development of digital identities, the concept of self-sovereign identity enables people to gain verifiable identities apart from any government. Instead, information and credentials about a person could be issued by private corporations and, as already mentioned, by any social grouping.
A future marked by a multitude of legal entities, any or all of which could provide reliable identification, could ease the emergence of a non-centralized cryptoeconomy. Already today, public blockchains as independent settlement networks with neutral, non-state assets further an alternative economy. This economy is not only about earning opportunities apart from big corporations, traditional workplaces, and tax offices. There is also the possibility of generating income on the blockchain with emerging, decentralized, financial protocols. Income generated in this new second realm could easily be hidden from tax authorities, requiring ever more aggressive and alienating policing efforts by governments.
Digital identity remains the crucial, missing piece to allow this new counter-economy to really take off. Especially in the lending and borrowing business, credit transactions usually have to be overcollateralized. Borrowers cannot be held accountable because there is no real identity attached to them, making it hard to come up with things like credit scores that would give lenders more reassurance. Here again, self-sovereign identity holds great promise and could be a game-changer for reliable reputation management systems in this blockchain and decentralized finance world.
With identity being the missing link, the advent of self-sovereign identity could finally bring ambitious projects like Bitnation to fruition. This virtual blockchain jurisdiction wants to establish a blockchain-based self-administration or, as the project itself advertises, “a toolbox for do-it-yourself governance.” With the concept of self-sovereign identity being implemented properly, new digital nations such as Bitnation could compete against old territorial tax states. Competition from so-called “digital nations” would certainly put incompetent nation states under pressure. And digital nations, especially in conglomeration, would be marked by consent, voluntarism, and service-oriented behavior in contrast to the more coercive and controlling conduct of nation states.
In the face of enhanced competition, expect nation states to turn to heightened surveillance and attempts at appropriating new identity technologies. After all, progressive digitalization and technology development would also make it easier to monitor internet participants. From a libertarian perspective, that makes it all the more important that we understand how technologies like self-sovereignty identity could help us carve out new redoubts for liberty.